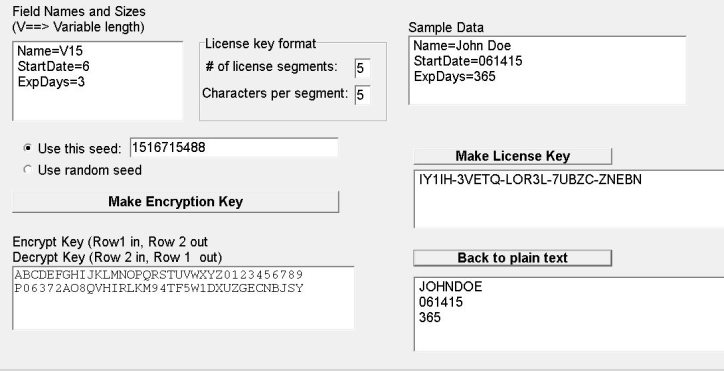
Enhanced key-generation algorithm using MRMCTT in Data encryption standard algorithm | Semantic Scholar
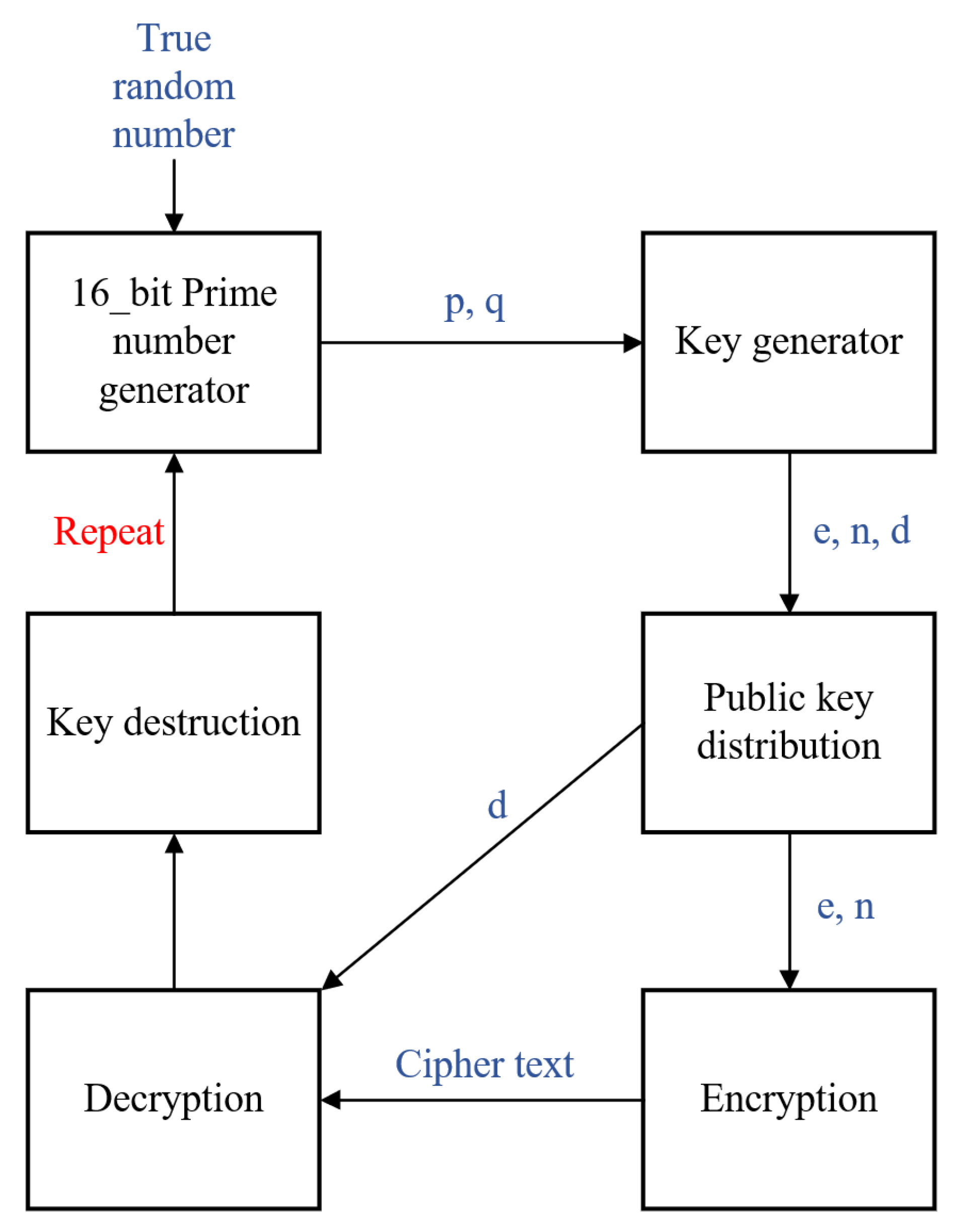
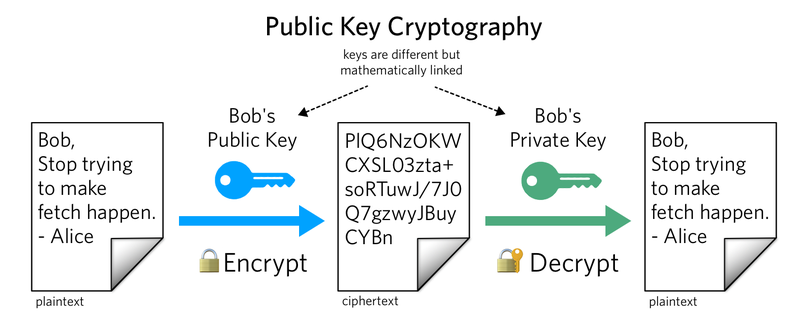
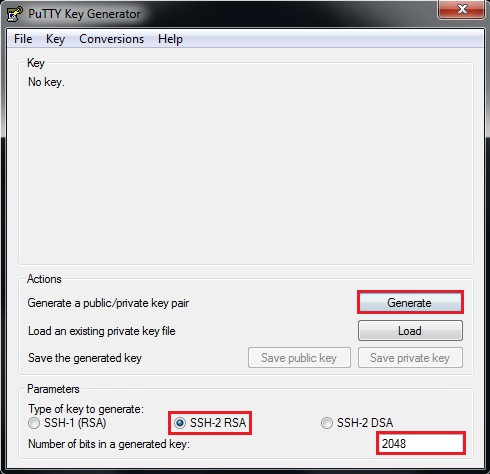
Electronics | Free Full-Text | New RSA Encryption Mechanism Using One-Time Encryption Keys and Unpredictable Bio-Signal for Wireless Communication Devices